Our products and packages solutions blend advanced technology with experience in operations across the harshest environments.
Products and Tech Solutions
Booz Allen offers a range of software platforms, analytical tools, and cybersecurity accelerators that seamlessly integrate today’s most advanced technology with bold thinking and unparalleled expertise. We specialize in designing intelligent, tailor-made solutions built to tackle the nation’s most critical missions.
Whether you’re looking to safeguard your AI systems against cyberattacks or harness and share real-time intelligence at the tactical edge, we have the tools, technology accelerators, and solutions to help you meet today’s challenges head-on. Working with us, you won’t just keep pace with the 21st century, you’ll take command of it. Please choose from the categories below to explore our offerings.
Featured Products
Outpace the threat. Reverse the unknown
Vellox Reverser
Booz Allen Vellox Reverser is an AI-first malware reverse engineering product that automates evasive malware analysis.


Situational Awareness in Real Time
Sit(x)®
Sit(x) delivers TAK-Server-as-a-Service to connect military, law enforcement, and first responders for shared operations.
See Our Technology Accelerators in Action
Empowering Missions at Scale
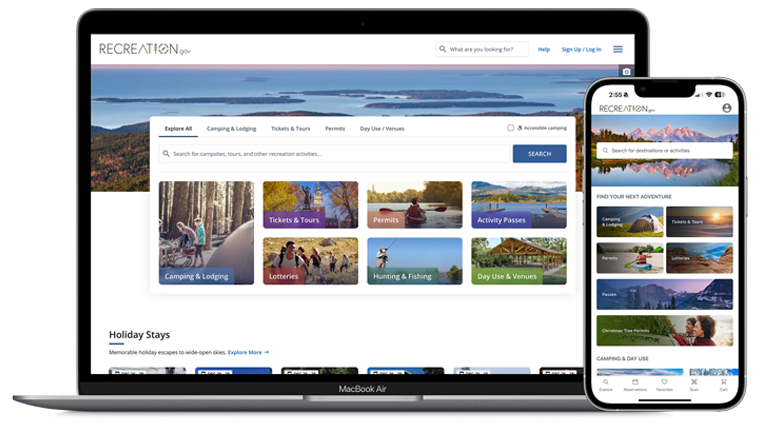
Recreation.gov
Working closely with stakeholders, we reinvented Recreation.gov by building a modern, scalable, cloud-native, e-commerce platform transforming how millions of visitors discover public lands. The new site is a one-stop shop for trip information, planning, and reservations from coast to coast.
Learn More about Booz Allen Products and Tech Solutions
Subscribe to our newsletter for the latest insights, thought leadership, and analysis.