Operational Technology (OT) Cybersecurity

The Outcome
As a result of our efforts, the client identified major network infrastructure issues and increased visibility of potentially malicious or risky behaviors within their manufacturing environment by 70%. The client now leverages one of the most mature secure manufacturing operations across the industry to generate true competitive advantages and considerable cost savings.

The Situation
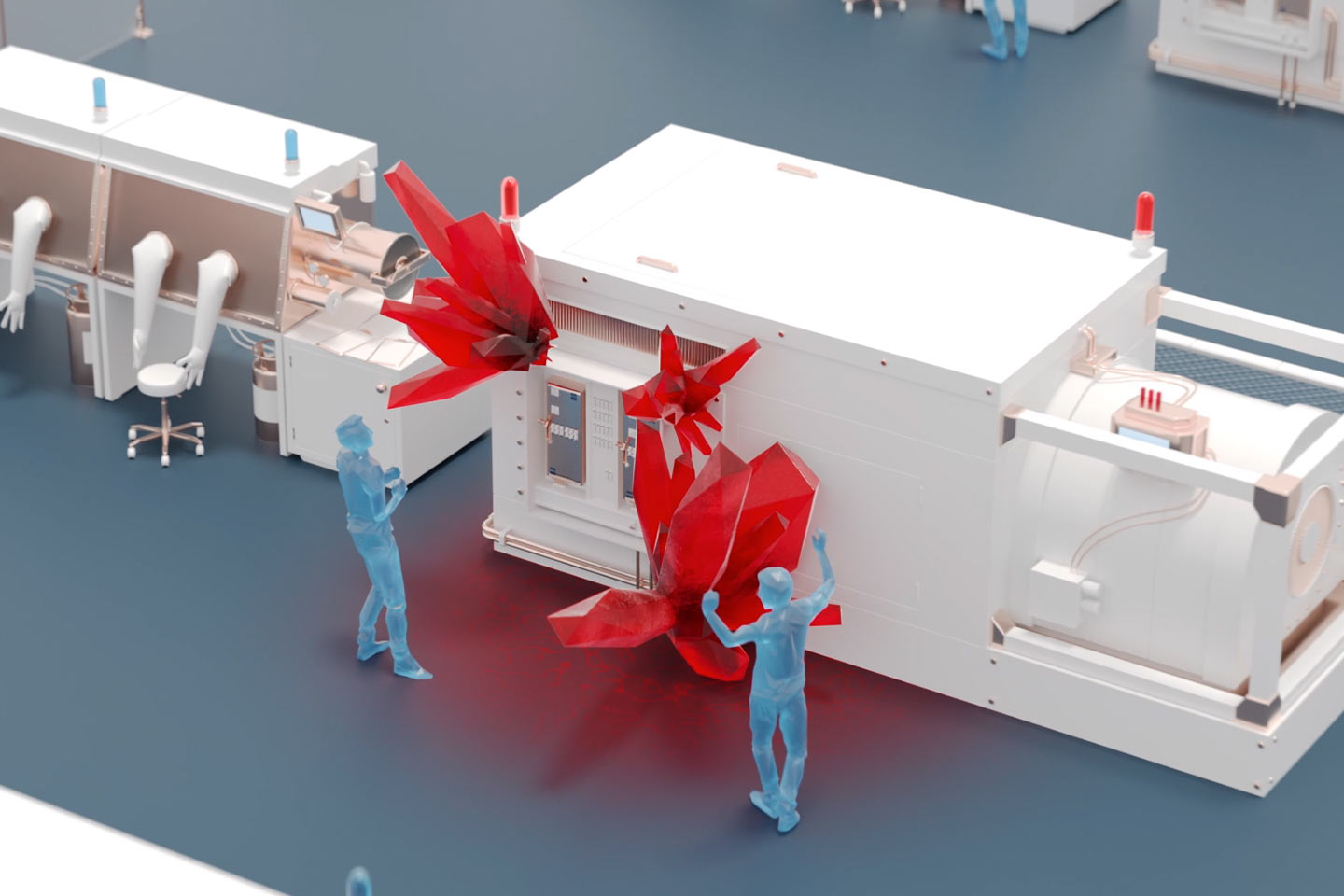
To support business-critical digital transformation initiatives, a Fortune 500 pharmaceutical company realized they needed to modernize the security of their manufacturing plants and global operations. The organization faced advanced cyber threats and suspected the presence of malware, which represented an existential threat to equipment that controlled the operations of critical, life-saving products.
The Approach

Booz Allen’s cybersecurity and manufacturing experts quickly identified security gaps across their manufacturing footprint, prioritizing OT assets. Simultaneously, we partnered with the client’s executive leadership to build a culture of relentless preparation, reconciling IT security requirements with an understanding of OT production pressures across the organization to ensure sustainable, long-term cybersecurity.